Cueing up a calculator: an introduction to exploit development on
Par un écrivain mystérieux
Description
Using CVE-2023-43641 as an example, I’ll explain how to develop an exploit for a memory corruption vulnerability on Linux. The exploit has to bypass several mitigations to achieve code execution.
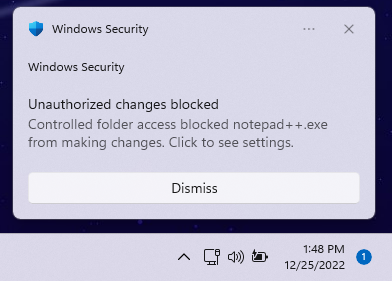
Microsoft Defender Antivirus: Most Up-to-Date Encyclopedia, News & Reviews
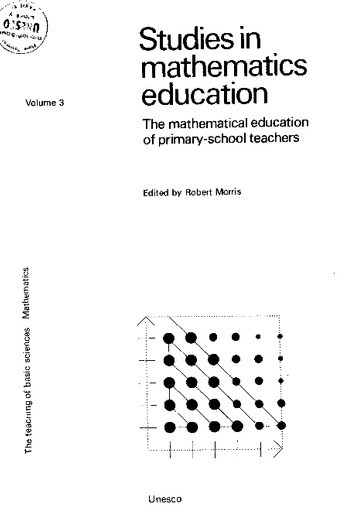
Informatics: implications of calculators and computers for primary-school mathematics

198269823 metasploit the penetration testers guide by M4st3rm1nd - Issuu

PentesterLab on LinkedIn: PentesterLab: White Badge

Blogs - CloudMoyo
Cueing up a calculator: an introduction to exploit development on Linux - The GitHub Blog

Scientific calculator project in c language
Zero Day Zen Garden: Windows Exploit Development - Part 1 [Stack Buffer Overflow Intro]

Free Course: CNIT 127: Exploit Development from CNIT - City College of San Francisco

Code complete, second edition ebookpart2 by Med Mes - Issuu
depuis
par adulte (le prix varie selon la taille du groupe)